Introducing: Chisel Operator for Kubernetes (Alpha)

We tech enthusiasts love self-hosting. And the most of us have one tiny issue that prevents us from achieving it: CGNAT.
Today we're running out of IPv4 addresses, and the reason is due to a a
mathematical error and a lack of foresight of our forefathers. We never knew that there would be so much people on the Internet. There are only 4.3 billion IP addresses, and a couple billion of them is monopolized by a group of big cloud providers.
Why am I talking about this? Well, nowadays your local ISP usually runs your home network behind a CGNAT. Essentially a massive subnet designed to serve thousands of customers, all running behind 1 public IP address. That means, they do not give you a publicly-accessible IPv4 address.
That means, you can no longer expose (port-forward) your home network to the internet. You can no longer run a website off your home modem like in the old days. And that also means it's now way harder to self-host your own services.
Fortunately, there's a concept known as reverse proxies: Establishing a connection to a separate, publicly accessible server and then redirecting all incoming connections from that server to your desired device.
Usually this is used to to route connections over local-area networks (hence port-forwarding) or over conventional VPNs. However, you can add an additional layer and instead of going through an existing network, you run another server that acts as a dedicated VPN, starting a new network exclusively for your device. This is called tunneling.
There are many various network tunneling solutions out there, with many different quirks of their own. And the well-known ones are:
- The good ol' ngrok, one of the first ever tunneling services out there. Made as a temporary way to quickly expose a website on the Internet. Primarily used for development purposes for web developers to try out their websites.
- Cloudflare Tunnel: One of the newer tunneling services out there. Created by the big online delivery service Cloudflare, It is a partially open-source tunneling solution designed for use cases slightly more demanding than ngrok. You can assign your own domain names to local services and serve them publicly. While they provide a blazing-fast connections and very low latencies, they actively discourage heavy usage of their services, and you risk vendor lock-in as you must only go through one of their proxies to access your website.
The both of these are great options if you just want to run a static website to show off your resume or make a cool personal exhibit to show off your creativity, but when you self-host, you usually run way more than those. And that's where the fully self-hosted tunneling solutions come in.
The most straightforward way to run your own tunnel is to rent a VPS from a cloud provider, install a VPN on both your source and destination machines, and wire them together. However, that's not really scalable. as you set up more and more services on your home lab and you have to keep routing more services and keep track of local IP addresses and ports, remembering what goes where.
Finding the perfect tunnel
At first, I found something called inlets. inlets was a seemingly great network tunnel that lets you bring your own server, then tunnel from your home to there and publicly exposes all your services behind that server.
However, the more I look into inlets, the worse it gets.
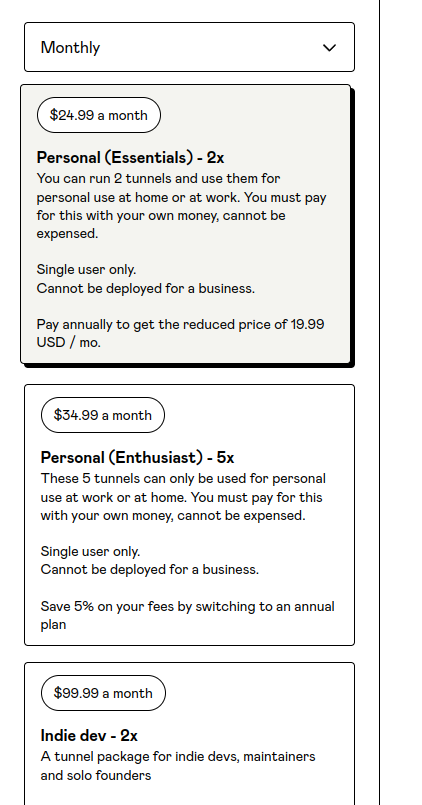
Due to the developer's insistence on trying to make a living out of inlets, he had a meltdown on Twitter and decided to completely wipe off the source code of inlets' OSS version off the face of the internet. And on top of that, the lowest-tier subscription costs a whopping twenty-five US dollars a month!
However, inlets itself was a really great tunneling solution. It had a Kubernetes operator and a cloud provisioner that integrates with many various cloud providers to automatically provision a new VPS for you for each load balancer.
After a long week of trying to find a better (and also friendly) alternative to inlets, I have completely failed to find anything that comes close to it. And that's where I decided to do it myself.
The Real Content
I've been working for a couple nights doing this as a side project, and we at Fyra Labs are very excited to introduce to you: The Chisel Operator for Kubernetes!
Chisel is a great network tunneling solution written in the Go programming language. It fully supports both TCP and UDP connections over SSH tunnels and even ACL via a JSON configuration file. We have a created a new Kubernetes operator to automatically forward ports on Kubernetes LoadBalancer services to a self-provisioned exit node. It's very easy to set up, you simply need:
- A VPS instance with a public IP address
- Any Kubernetes cluster
That's it! Simply install Chisel on your exit node, start it up as a service, Add that exit node to your cluster, and voila! Your cluster now has a load balancer on the cloud!
The alpha version allows you to simply add a Chisel tunnel server, secure it and then turn any internet-connected computer into a Kubernetes load balancer, albeit publicly or within your own private network.
We're planning to add many more features to the operator, including automatic cloud provisioning, multiple exit node support and more!
And on top of that, the operator code will be fully open-source, forever. We don't plan to make money on a tiny program that just deploys a pod for you.
We hope you find our new product useful, and have a nice day.


Comments ()